Cybersecurity News
Stay informed about the latest cybersecurity incidents, vulnerabilities, and threat landscape changes. We cover data breaches, ransomware campaigns, critical CVEs, and regulatory updates – with context on what it means for you and how to protect yourself.
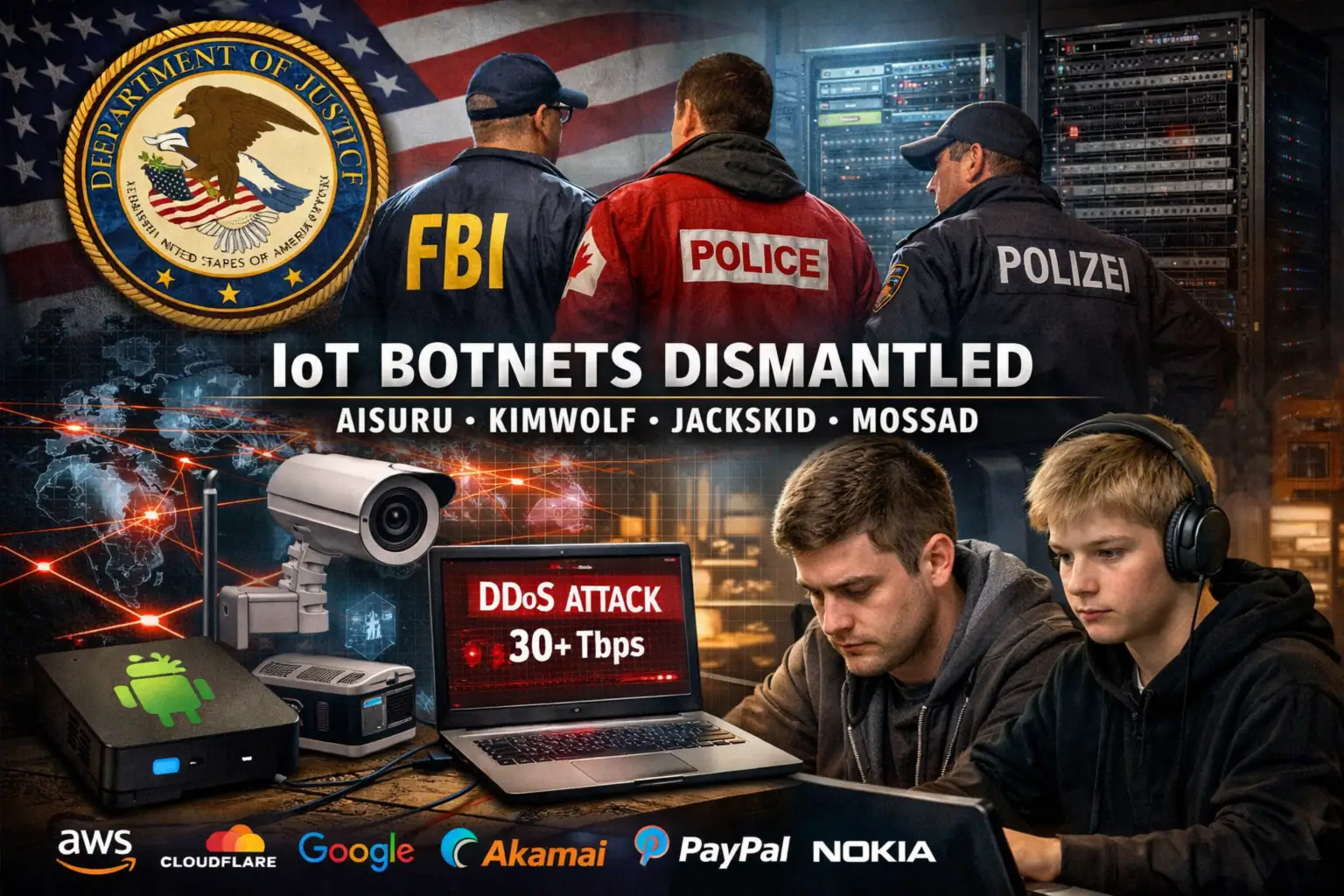
US Justice Department Disrupts Massive IoT Botnets Behind Record-Breaking DDoS Attacks
The US Department of Justice (DoJ) has led a large‑scale operation to disrupt the command‑and‑control (C2) infrastructure of several major ...
Eight AWS Bedrock Attack Vectors: Securing Enterprise AI Beyond the Model
AWS Bedrock is rapidly becoming a core foundation for enterprise AI applications, giving organizations managed access to foundation models and ...

Quest KACE SMA CVE-2025-32975: Critical Authentication Bypass Under Active Attack
Corporate networks are facing active exploitation of CVE-2025-32975, a critical authentication bypass vulnerability in the Quest KACE Systems Management Appliance ...

Apple Security Alert: Coruna and DarkSword Exploits Target Outdated iOS Devices
Apple has released a security warning for iPhone users who continue to run outdated versions of iOS. According to the ...

Global Takedown of Aisuru, Kimwolf, JackSkid and Mossad IoT DDoS Botnets
Law enforcement agencies in the United States, Germany and Canada have carried out a coordinated operation against four of the ...

CVE-2026-3888 in Ubuntu 24.04: snapd Vulnerability Enables Local Privilege Escalation
A new high-severity vulnerability, CVE-2026-3888, has been identified in Ubuntu Desktop 24.04 and newer, allowing a local, unprivileged attacker to ...

Stryker Cyberattack: How Hackers Used Microsoft Intune to Wipe 80,000 Devices
A significant cybersecurity incident in the medical technology sector has hit global medtech manufacturer Stryker, where attackers remotely erased data ...

Perseus Android Banking Trojan Targets Note‑Taking Apps to Steal Passwords and Seed Phrases
A new Android banking trojan dubbed Perseus is setting a concerning precedent in mobile malware. According to research by ThreatFabric, ...

DarkSword iOS Exploit Kit: Safari-Based Spyware Threat Puts Millions of iPhones at Risk
Security researchers from Lookout, iVerify and Google’s Threat Intelligence Group (GTIG) have uncovered a new advanced iOS exploit kit dubbed ...







