CyberSecurity Blog
More
Essentials of Cybersecurity
Red Teamer: How to Become an Elite Offensive Security Specialist
In the dynamic world of information security, there exists an elite group of professionals who are legally authorized to hack …
Most popular
Cybersecurity News
More
War Thunder Classified Military Data Leak: Ninth Security Incident Exposes NATOPS Manual
CyberSecureFox 🦊
The popular military simulation game War Thunder has experienced its ninth documented classified information leak, …

Critical Printer Security Vulnerabilities Expose 748 Models Across Major Manufacturers
CyberSecureFox 🦊
Cybersecurity researchers at Rapid7 have uncovered a comprehensive set of security vulnerabilities affecting 748 printer …

Critical macOS Shortcuts Vulnerability Allows Complete System Compromise
CyberSecureFox 🦊
Cybersecurity researchers at Positive Technologies have uncovered a severe security vulnerability in Apple’s Shortcuts application …
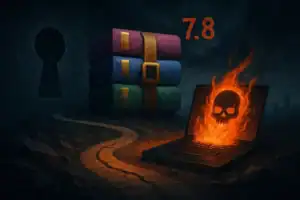
Critical WinRAR Vulnerability CVE-2025-6218 Allows Remote Code Execution Through Path Traversal Attack
CyberSecureFox 🦊
WinRAR developers have released an emergency security update to address a critical vulnerability CVE-2025-6218 that …









