Cybersecurity News
Stay informed about the latest cybersecurity incidents, vulnerabilities, and threat landscape changes. We cover data breaches, ransomware campaigns, critical CVEs, and regulatory updates – with context on what it means for you and how to protect yourself.

Critical GnuTLS Use-After-Free Vulnerability in Exim (CVE-2026-45185)
The Exim project has released an emergency security update that fixes the CVE-2026-45185 use-after-free vulnerability, which leads to heap corruption ...
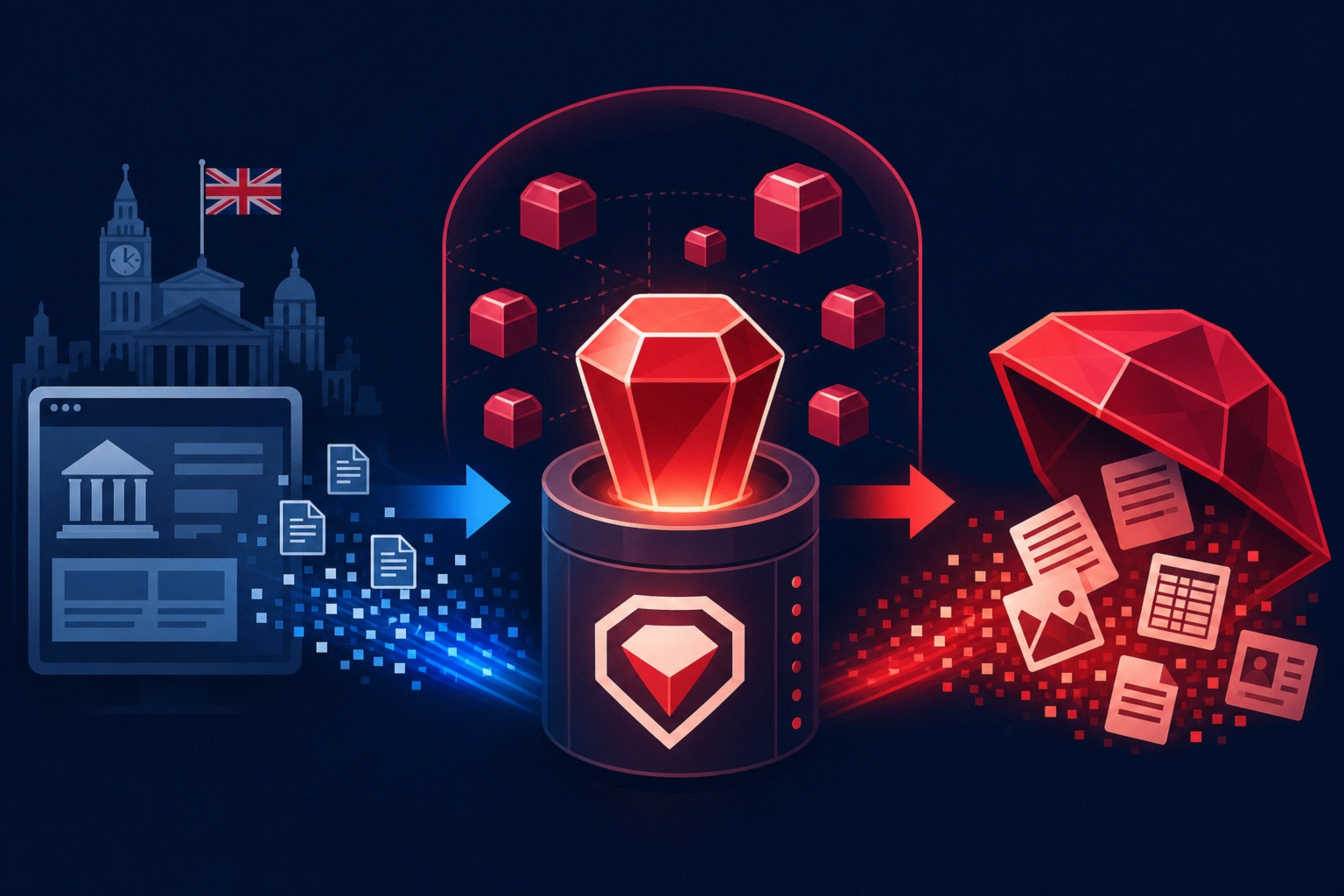
GemStuffer campaign turns RubyGems into free data infrastructure
Researchers at Socket discovered a campaign called GemStuffer, in which more than 150 packages were uploaded to the RubyGems repository ...

How Microsoft’s May 2026 Patch Tuesday Impacts Windows, Azure and AD
Microsoft in the May Patch Tuesday 2026 closed 138 vulnerabilities in Windows and cloud services, including critical flaws in Windows ...

Inside QLNX: a stealthy Linux implant stealing developer secrets
Trend Micro researchers have described a previously undocumented Linux implant codenamed Quasar Linux RAT (QLNX), which, according to their findings, ...

How Low-Priority Alerts and EDR ‘Mitigations’ Hide Real Threats
A study covering more than 25 million security alerts in real corporate environments revealed a structural issue: almost 1% of ...

Critical PAN-OS buffer overflow in User-ID portal under attack
Palo Alto Networks has confirmed limited active exploitation of the critical vulnerability CVE-2026-0300 in its PAN-OS software. This buffer overflow ...

vm2 sandbox escapes raise concerns over JavaScript isolation
Critical vulnerabilities have been discovered in the vm2 library, a popular tool for running untrusted JavaScript code in an isolated ...

Flare.io details PamDOORa PAM backdoor for persistent SSH access
Researchers at Flare.io have disclosed details of a new Linux backdoor called PamDOORa, which is reportedly being sold on the ...
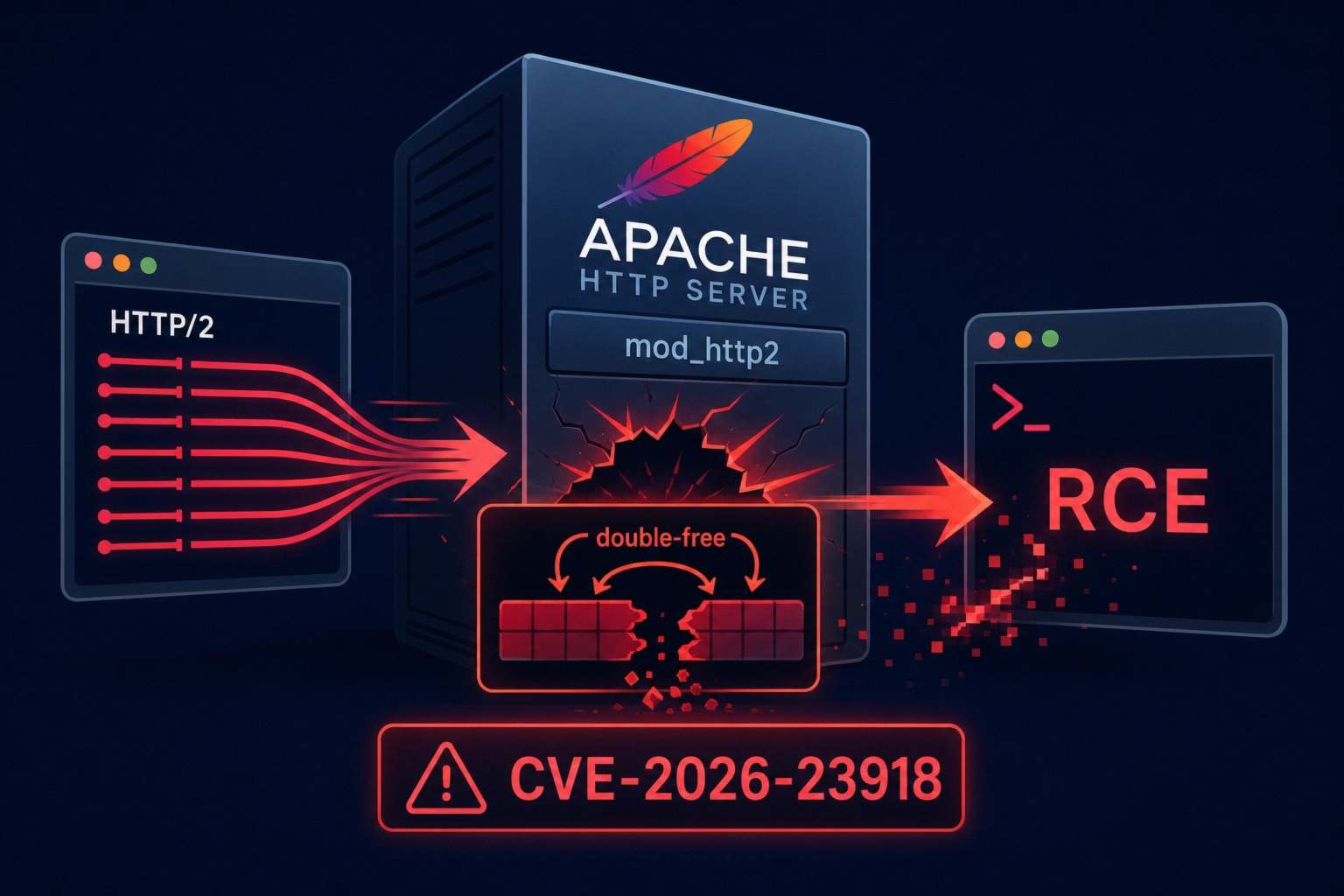
CVE-2026-23918: critical Apache HTTP/2 flaw and mitigation guidance
Apache Software Foundation has released a security update for Apache HTTP Server that fixes a critical vulnerability CVE-2026-23918 (CVSS 8.8) ...

New xlabs_v1 Mirai Botnet Exploits Android ADB for DDoS Attacks
Researchers from Hunt.io have discovered a new botnet based on Mirai, identifying itself as xlabs_v1, which exploits devices with an ...






