Cybersecurity News
Stay informed about the latest cybersecurity incidents, vulnerabilities, and threat landscape changes. We cover data breaches, ransomware campaigns, critical CVEs, and regulatory updates – with context on what it means for you and how to protect yourself.

Drift OAuth Token Theft Expands Beyond Salesforce, Impacts Google Workspace; Mandiant Ties Activity to UNC6395
Google Threat Intelligence (Mandiant) has linked a wave of intrusions to the theft and reuse of OAuth and refresh tokens ...
FreePBX Zero‑Day (CVE-2025-57819) Exploited in the Wild: What to Do Now
Sangoma Technologies has confirmed in-the-wild exploitation of a critical zero‑day in FreePBX, the open-source PBX platform built on Asterisk and ...

Critical Vulnerabilities in Pudu Robotics’ Service Robots Exposed and Remediated
An independent security researcher known as BobDaHacker disclosed critical weaknesses in the Pudu Robotics ecosystem that could allow attackers to ...
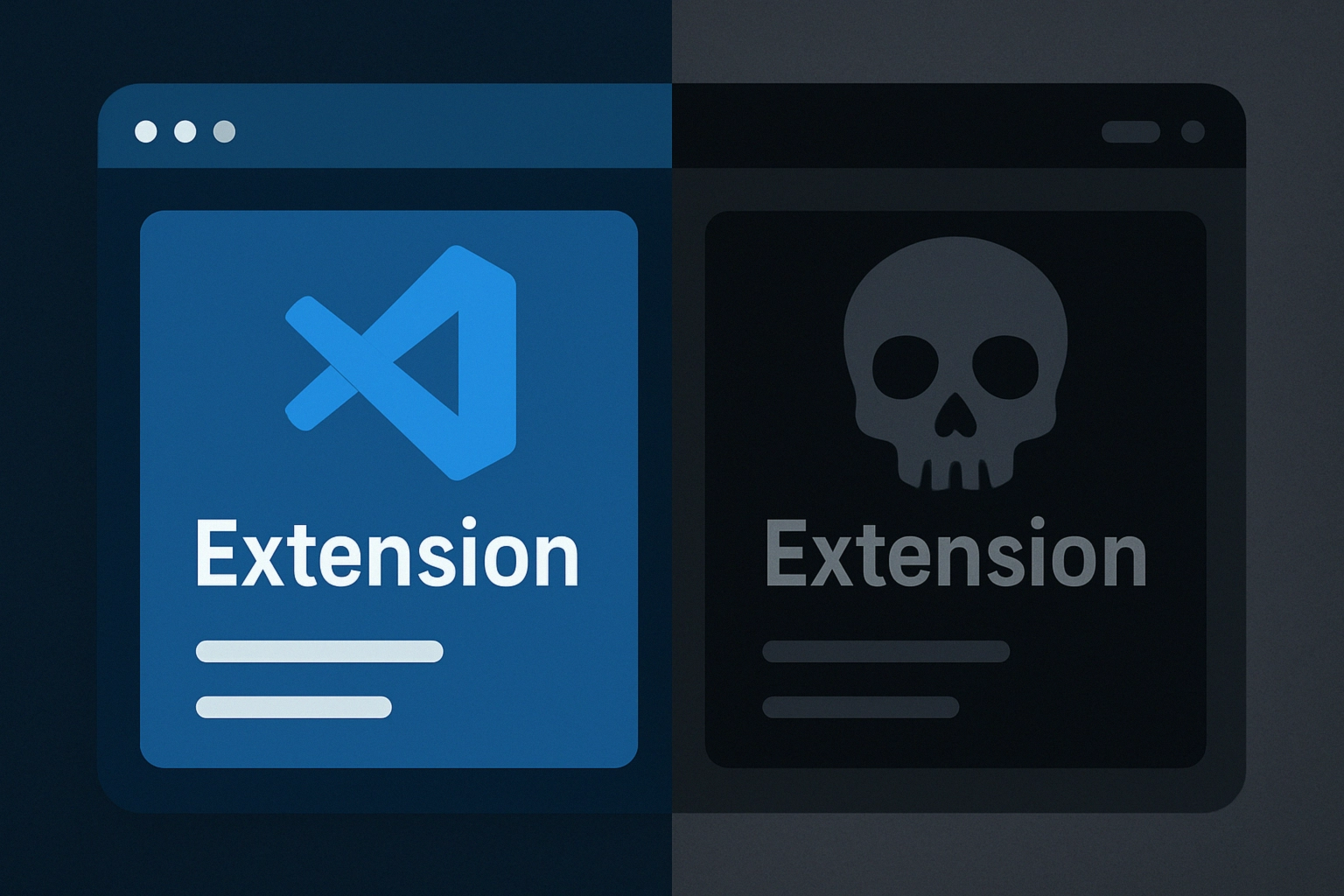
VS Code Marketplace Name Reuse Opens Door to Brandjacking and Malware Loaders
ReversingLabs has identified an integrity gap in the Visual Studio Code Marketplace: when an extension is hard-deleted, its name can ...

Jaguar Land Rover Confirms Cyber Incident: Operations Disrupted, Customer Data Unaffected
Jaguar Land Rover (JLR) has confirmed a cyber incident that prompted the company to proactively take a portion of its ...

Cloudflare Thwarts Record 11.5 Tbps DDoS as UDP Flood Hits 5.1 Billion PPS
Cloudflare reports neutralizing the largest hyper‑volumetric distributed denial‑of‑service (DDoS) attack observed to date, with peak bandwidth hitting 11.5 Tbps and ...

Hacktivists and Three Threat Clusters Are Shaping Attacks on Russia, Belarus, and Neighboring States
Kaspersky researchers have released a technical review of 14 threat groups most actively targeting organizations in Russia, Belarus, and several ...

Salesloft Drift OAuth Attack Exposes Salesforce Data at Major Firms
A large-scale supply-chain intrusion involving the Salesloft Drift integration platform led to the theft of OAuth and refresh tokens and ...

Adversaries Turn Velociraptor into a LotL Weapon via msiexec and VS Code Tunnels
Sophos Counter Threat Unit has observed a campaign where attackers weaponized the open‑source digital forensics and incident response (DFIR) tool ...

HexStrike AI Chatter Fuels Rapid n‑Day Exploitation of Citrix NetScaler CVEs
Check Point analysts warn that threat actors are discussing the use of HexStrike AI to accelerate exploitation of recent n‑day ...