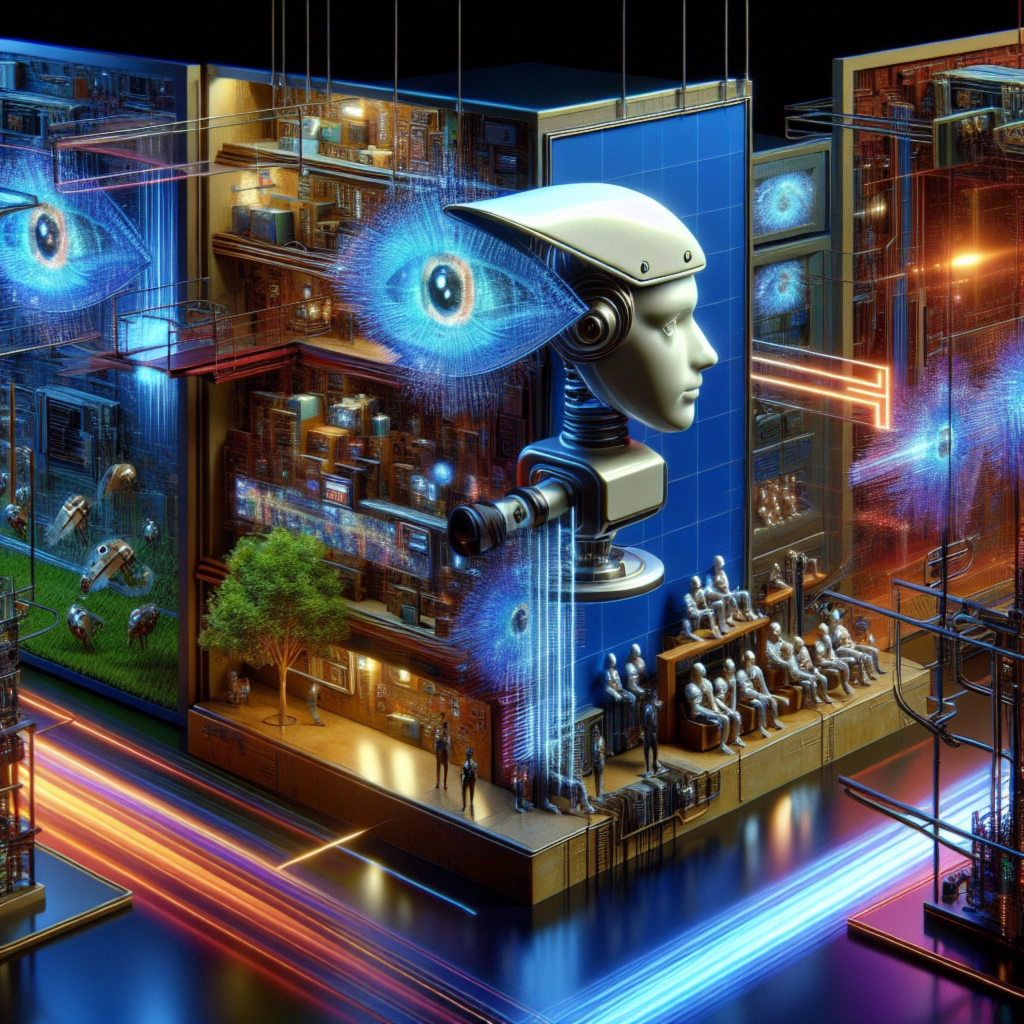
Cybersecurity News
Stay informed about the latest cybersecurity incidents, vulnerabilities, and threat landscape changes. We cover data breaches, ransomware campaigns, critical CVEs, and regulatory updates – with context on what it means for you and how to protect yourself.

Casio Cyberattack: Underground Ransomware Group Claims Responsibility
On October 5, 2024, Japanese electronics giant Casio experienced a significant cybersecurity breach, disrupting several systems and services. The incident, ...

Advanced Phishing Campaign Exploits ESET Partner Infrastructure in Israel
On October 8, 2024, a sophisticated phishing campaign targeting ESET customers in Israel was uncovered, showcasing the evolving complexity of ...

Bohemia and Cannabia Darknet Marketplaces Shut Down: Admins Caught, Millions Seized
In a significant blow to the darknet ecosystem, an international law enforcement operation has resulted in the arrest of two ...

Microsoft Announces End of Support for PPTP and L2TP VPN Protocols
In a significant move to bolster cybersecurity, Microsoft has announced plans to discontinue support for two long-standing VPN protocols: Point-to-Point ...

Mozilla Releases Emergency Patch for Firefox: Critical Use-After-Free Vulnerability Exploited in the Wild
Mozilla has released an urgent security update for its Firefox browser, addressing a critical vulnerability that has been actively exploited ...

Lego Website Compromised: Cybercriminals Promote Fake Cryptocurrency Token
In a recent cybersecurity incident, the official Lego website fell victim to a sophisticated attack, highlighting the ongoing threats faced ...

Game Freak Data Breach: Pokemon Developer Acknowledges Security Incident
In a concerning development for the gaming industry, Game Freak, the renowned Japanese video game developer and co-owner of the ...

Cybersecurity Alert: Awaken Likho Group Evolves Attack Methods on Russian Organizations
Kaspersky Lab has reported a significant evolution in the tactics employed by the hacker group Awaken Likho, also known as ...
OpenAI Uncovers and Blocks Malicious Use of ChatGPT by Hacker Groups
In a recent report, OpenAI revealed that it has successfully prevented over 20 foreign “influence operations” that were exploiting ChatGPT ...

Verizon Push-to-Talk Data Breach: Implications for Government and Emergency Services
A significant cybersecurity incident has come to light, involving the compromise of Verizon’s Push-to-Talk (PTT) systems, which are widely used ...






