Cybersecurity News
Stay informed about the latest cybersecurity incidents, vulnerabilities, and threat landscape changes. We cover data breaches, ransomware campaigns, critical CVEs, and regulatory updates – with context on what it means for you and how to protect yourself.

ScarCruft targets sqgame[.]net users with BirdCall spyware
The North Korea–linked group ScarCruft carried out a targeted supply-chain attack against the gaming platform sqgame[.]net, popular among ethnic Koreans ...
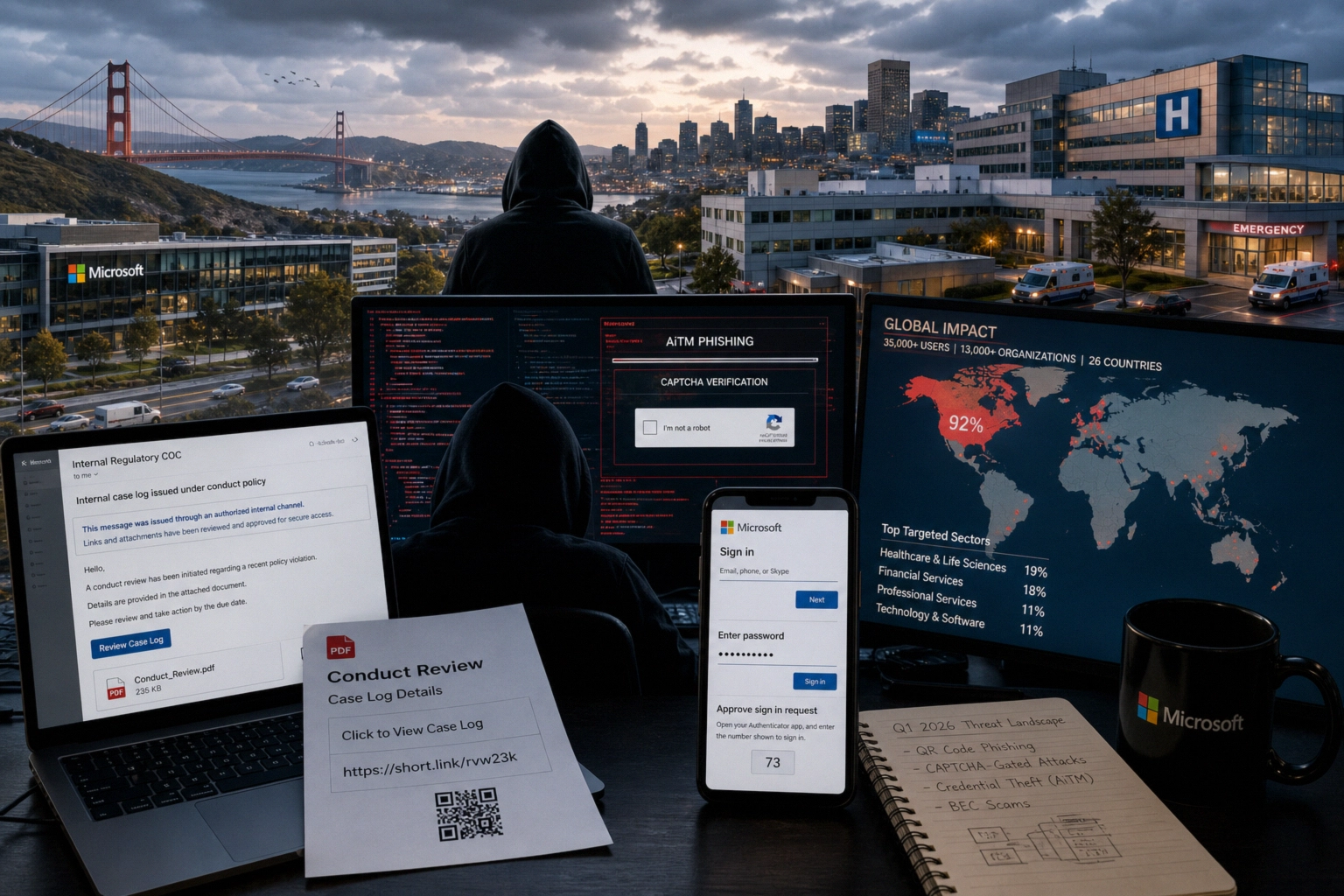
How a Multi‑Stage AiTM Phishing Campaign Bypasses MFA and Targets 35,000 Users
In mid‑April 2026, a multi‑stage phishing campaign was identified that targeted more than 35,000 users across 13,000 organizations. It used ...

Patches for Critical MOVEit Automation Auth Bypass and Privilege Bugs
Progress Software has released updates to address two vulnerabilities in MOVEit Automation, one of which is the critical authentication bypass ...

AI-Driven Cyberattacks, Supply Chain Threats and Defense Tactics
In 2025, the barrier to entry for sophisticated cyberattacks collapsed: teenagers with no technical skills, using systems based on large ...

How global raids on pig butchering scams reshape crypto risk
An international operation involving the US, China, and the UAE led to the arrest of at least 276 people, the ...

Shadow-Earth-053, ShadowPad and phishing clusters in Asia
Researchers have recorded a new China-aligned espionage activity cluster, SHADOW-EARTH-053, targeting government and defense organizations in South, East and Southeast ...

Copy Fail (CVE-2026-31431): Linux Kernel LPE Actively Exploited
CISA has added the CVE-2026-31431 (Copy Fail) vulnerability in the Linux kernel to its CISA KEV Known Exploited Vulnerabilities catalog, ...

VECT 2.0 Ransomware: Critical Encryption Flaw Turns RaaS into a Data-Wiping Wiper
Recent analysis of the VECT 2.0 ransomware family reveals a critical design flaw that effectively transforms this ransomware-as-a-service (RaaS) operation ...








